Selecting the right open-source table format is about securing your infrastructure strategy. Making the right choice helps you save development costs and minimize risks. A well-chosen format lowers your Total Cost of Ownership (TCO) and ensures a future-proof, sustainable architecture. Let’s dive into three popular formats, so you can quickly deliver results without getting locked into a bad ecosystem.
Open table formats bring database-like ACID transactions to your data lake. They reduce storage costs by minimizing data duplication. Here is how Iceberg, Delta, and Hudi compare on the technical essentials.
The Battle of Table Formats: Iceberg vs Delta vs Hudi
Stop risking costly vendor lock-in and future-proof your data lakehouse today. In this deep dive, we cut through the noise to compare the big three open table formats: Apache Iceberg, Delta Lake, and Apache Hudi. We’ll analyze infrastructure fit, real-world performance, and Data Vault integration to help you drive down your TCO. Join us to find the exact format your architecture needs—before you commit to an expensive, irreversible path. Learn more in our upcoming webinar on May 19th, 2026!
Performance Under Pressure
Performance depends directly on your compute engine and use case. Delta Lake is highly optimized for Apache Spark, providing efficient read performance for Spark-heavy workloads. Apache Hudi is specifically built for streaming-first architectures that require handling massive amounts of updates and deletes (upserts). Apache Iceberg utilizes an engine-agnostic architecture, maintaining consistent query performance across multiple different engines like Trino, Flink, and Spark.
It is important to note that choosing the query engine is more important than the table format itself. A well calibrated format-engine pair will perform similarly well.
Community Support
Community maturity directly impacts long-term risk minimization. Delta Lake is supported by a large user base, primarily driven by Databricks. Apache Iceberg currently holds the ultimate multi-vendor momentum. It receives active contributions from multiple major cloud providers and data vendors, offering broad ecosystem support. Apache Hudi’s community centers on data engineering for real-time ingestion and streaming pipelines.
Time Travel Capabilities
Time travel enables querying historical data, auditing changes, or reverting accidental deletions, serving as a critical mechanism for risk minimization. All three formats offer some type of “time travel”.
Delta uses a straightforward transaction log. It replays JSON commits and Parquet checkpoints to reconstruct a table’s exact state at a specific timestamp or version.
Iceberg uses a tree of immutable metadata snapshots. Instead of processing a heavy transaction log, a query references a past snapshot ID. This approach scales efficiently for massive tables without performance degradation.
Hudi tracks changes via a chronological action timeline. It maintains a granular history of operations, enabling strict point-in-time queries that map directly to its streaming architecture.
Interoperability
Infrastructure strategy must account for evolving workloads. The industry is currently shifting toward cross-format compatibility. Projects like Apache XTable and Delta UniForm act as interoperability layers. Data written in one format (e.g., Delta) can be read natively as Iceberg or Hudi. This reduces vendor lock-in risks and lowers pipeline reengineering costs. Additionally, Apache Paimon offers an alternative for dynamic tables with native Apache Flink integration for high-throughput streaming workloads.
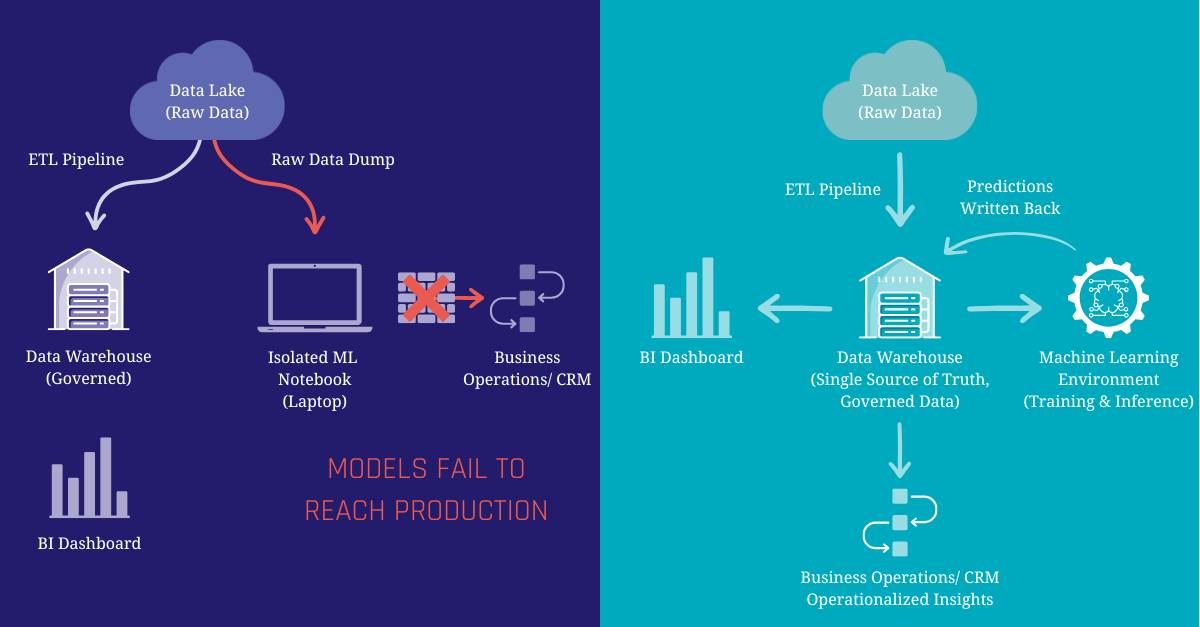
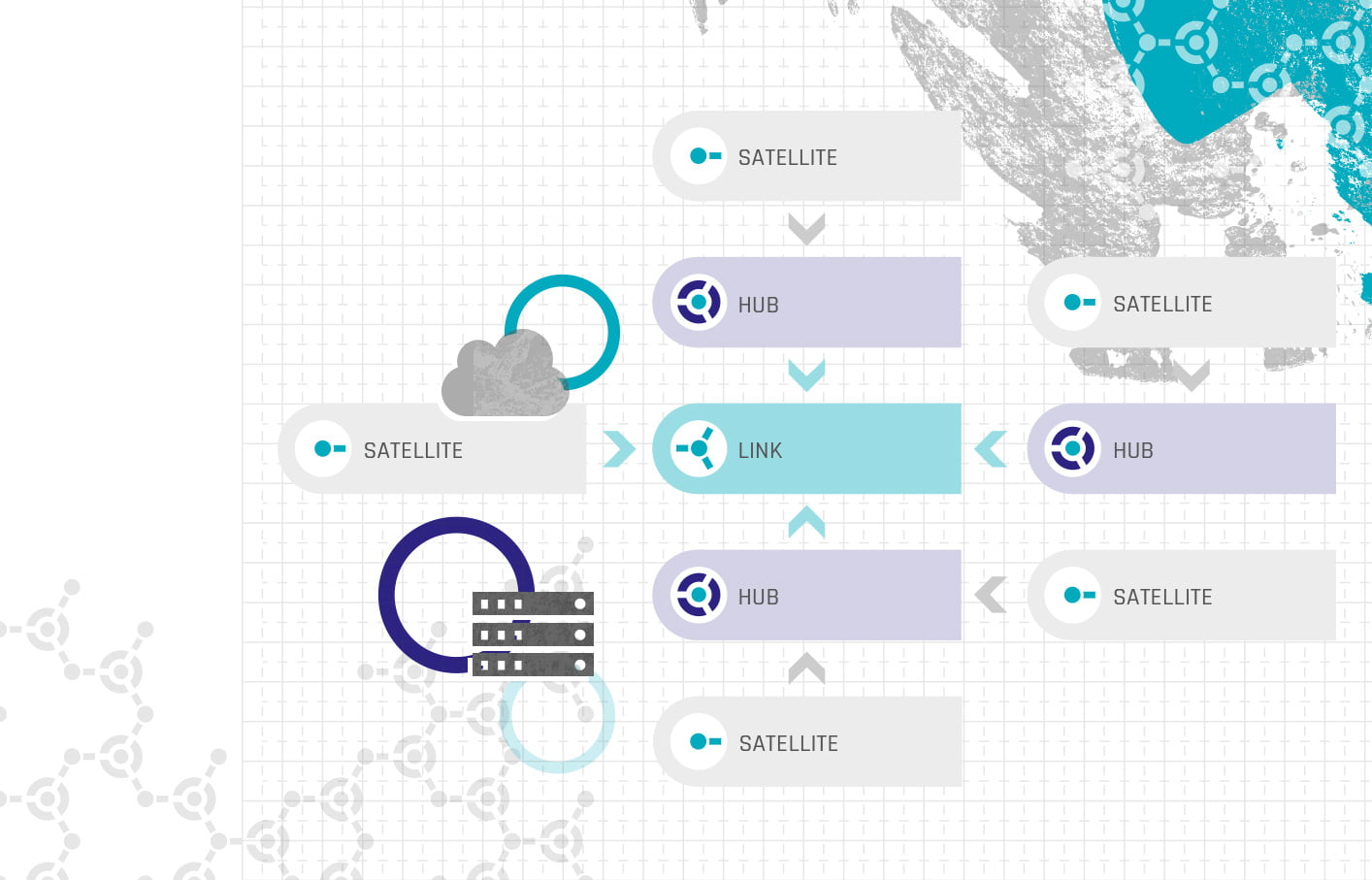
Architecture Insight: Data Vault
Table formats and modeling methodologies like Data Vault 2 are complementary. While Iceberg, Delta, or Hudi provide the optimized storage layer and ACID transactions, Data Vault provides the business alignment and agility. For optimal performance on a Data Lakehouse, you can materialize your Raw Vault core entities as physical Delta or Iceberg tables to serve as high-speed indexes. Furthermore, while table “time travel” is useful for quick rollbacks, long-term enterprise historization should still rely on Data Vault’s insert-only architecture to prevent data loss during routine storage maintenance.
A note on Time Travel vs. Historization: While format-level “time travel” is useful for quick rollbacks, long-term enterprise historization should still rely on Data Vault’s insert-only architecture. Relying solely on table formats risks permanent data loss during routine storage maintenance, such as Delta’s VACUUM command.
Keypoints for your Data Strategy
- Choose Delta for deep Spark integration.
- Choose Iceberg for maximum tool flexibility and a massive open ecosystem.
- Choose Hudi for heavy streaming and continuous upserts.
There is no single winner in the battle of table formats, only the right tool for your specific infrastructure strategy. By aligning your choice with your engine preference and streaming needs, you ensure high team agility and keep storage costs manageable.